- Jul 27, 2020
- 18,530
- 12,453
- 146

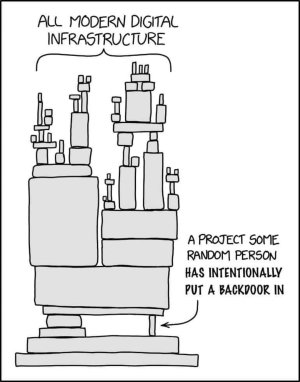
What we know about the xz Utils backdoor that almost infected the world
Malicious updates made to a ubiquitous tool were a few weeks away from going mainstream.
Everything I know about the XZ backdoor
Please note: This is being updated in real-time. The intent is to make sense of lots of simultaneous discoveries
boehs.org
Just frickin' unfathomable. How do serious developers get into a situation like that? It's like there is no proper protocol for verifying what a new version of a software does and if it doesn't introduce any undesirable side effects or worse, deliberate security holes to deliver future payloads! The entire opensource thing seems to be based on implicit trust. Everyone saw those malicious individuals (Jia and Jigar) as nothing out of the ordinary. Jigar bitching about some stable software not getting updates and the maintainer just agreeing with him? Who the hell is a stranger to tell a hobbyist maintainer of a widely used piece of software that there aren't enough updates? Collins should've told Jigar to F the hell off! The whole thing just makes me furious beyond words.