Jaskalas
Lifer
Updated 2018-01-05
CNN: Major chip flaws affect billions of devices
Testing Windows 10 performance after patching for "meltdown".
Results: mostly minor impact for end users.
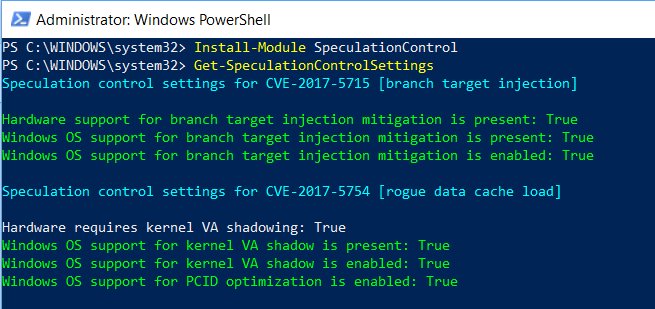
Current question, does the public have security patches to protect against Spectre yet?
Original Post:
CNN: Major chip flaws affect billions of devices
- Cnet: Spectre and Meltdown: Details you need on those big chip flaws
- Anandtech: Understanding Meltdown & Spectre
- Arstechnica: Here’s what Intel, Apple, Microsoft, others are doing about it
Testing Windows 10 performance after patching for "meltdown".
Results: mostly minor impact for end users.
Current question, does the public have security patches to protect against Spectre yet?
Original Post:
https://www.theregister.co.uk/2018/01/02/intel_cpu_design_flaw/
Programmers are scrambling to overhaul the open-source Linux kernel's virtual memory system. Meanwhile, Microsoft is expected to publicly introduce the necessary changes to its Windows operating system in an upcoming Patch Tuesdayhttps://hothardware.com/news/intel-cpu-bug-kernel-memory-isolation-linux-windows-macosCrucially, these updates to both Linux and Windows will incur a performance hit on Intel products. The effects are still being benchmarked, however we're looking at a ballpark figure of five to 30 per cent slow down, depending on the task and the processor model.
PSA, this could have some significant ramifications for both security and performance. If the story checks out, we're talking one busy month of major security patches.
Last edited: