Indeed AMD has, and indeed ARM is potentially becoming more relevant again with the merger with Xilinx. Xlinix just joined the Confidental Computing Consortium, in its introduction to it it writes (my bolding):
"
Confidential Computing can be achieved by assembling a TEE entirely in hardware. The three major CPU platform vendors: Intel, AMD, and ARM, all support a TEE. Intel has produced Software Guard Extensions (SGX), AMD’s offered up Secure Encrypted Virtualization (SEV), and ARM has TrustZone. Developers can leverage these TEE platforms, however, each is different, meaning code written for SGX will not work on an AMD processor. So, where does Xilinx fit in? Our objective is to understand how we can extend a TEE into an accelerator card or provide a method to securely hand off data and code between a host TEE and one executing within the accelerator card.
At this point, our Data Center Group (DCG) is exploring two paths. First, through our strong alliance with AMD, and we are exploring SEV to better understand how it might map to DCG’s future accelerator product plans. The second path involved our licensing of ARM core designs, which are included in many of our chips to handle control plane tasks. ARM has several other research projects underway that they’ve proposed to CCC that further extend TrustZone in ways that might make it much easier for us to secure an accelerator card’s execution environment. We’ve already begun discussions with the ARM team and hope to learn more over the coming months as we start to formulate our security plans for the future."

forums.xilinx.com
And just to note again, in all Zen chips AMD uses ARM for the control plane tasks as well, including offering ARM's TrustZone.
While not inaccurate in that article, TEE and SEV are totally different things. You will find TEE in all modern ARM SoCs used in mobile, automotive etc.
TEE allows a secure enclave which an application can access to do certain things without accessing the underlying secrets. A very common usage of TEE for example is storing private keys, API keys etc. For example, an application request a chunk of data to be signed using the private keys from the enclave but have no access to the private keys in question, but only gets the signed data. Therfore, very common use of TEE is in DRM, payment methods etc. It protect secrets on the host not the app. If you are developing consumer devices in some way or the other you would have likely needed to use TEE in some way.
A comparable implementation of TEE for Windows desktop would be the upcoming Microsoft Pluton IP.
SEV on the other hand protects VMs (and also processes) from one another by implementing control of context registers, process memory pages etc from within the process. SEV-SNP extends this to IOMMU and others.
In SEV-SME, the memory is encrypted using keys owned by the process, the host cannot access it. WITH SEV-ES host cannot access the paged memory, or influence DMA, or read registers owned by the process. A HW exception is triggered when such things happen and the guest will have to handle these exceptions which they can either terminate or log or send info somewhere else.
There is no equivalent to SEV as far I know. SGX and FME attempts to do part of it, but SEV is far more comprehensive. SEV-SNP is taking this even further.
SEV is unique tech, and for those who are in the server world, who are running their apps in public cloud knows how important this is.
AMD's PSP can aid the implementation of TEE, but by itself does much more than just that. It checks microcode signature, firmware signature, authenticate nodes attached to a system fabric etc. PSP is not involved in SEV in anyway. The SEV logic is built in the core itself.
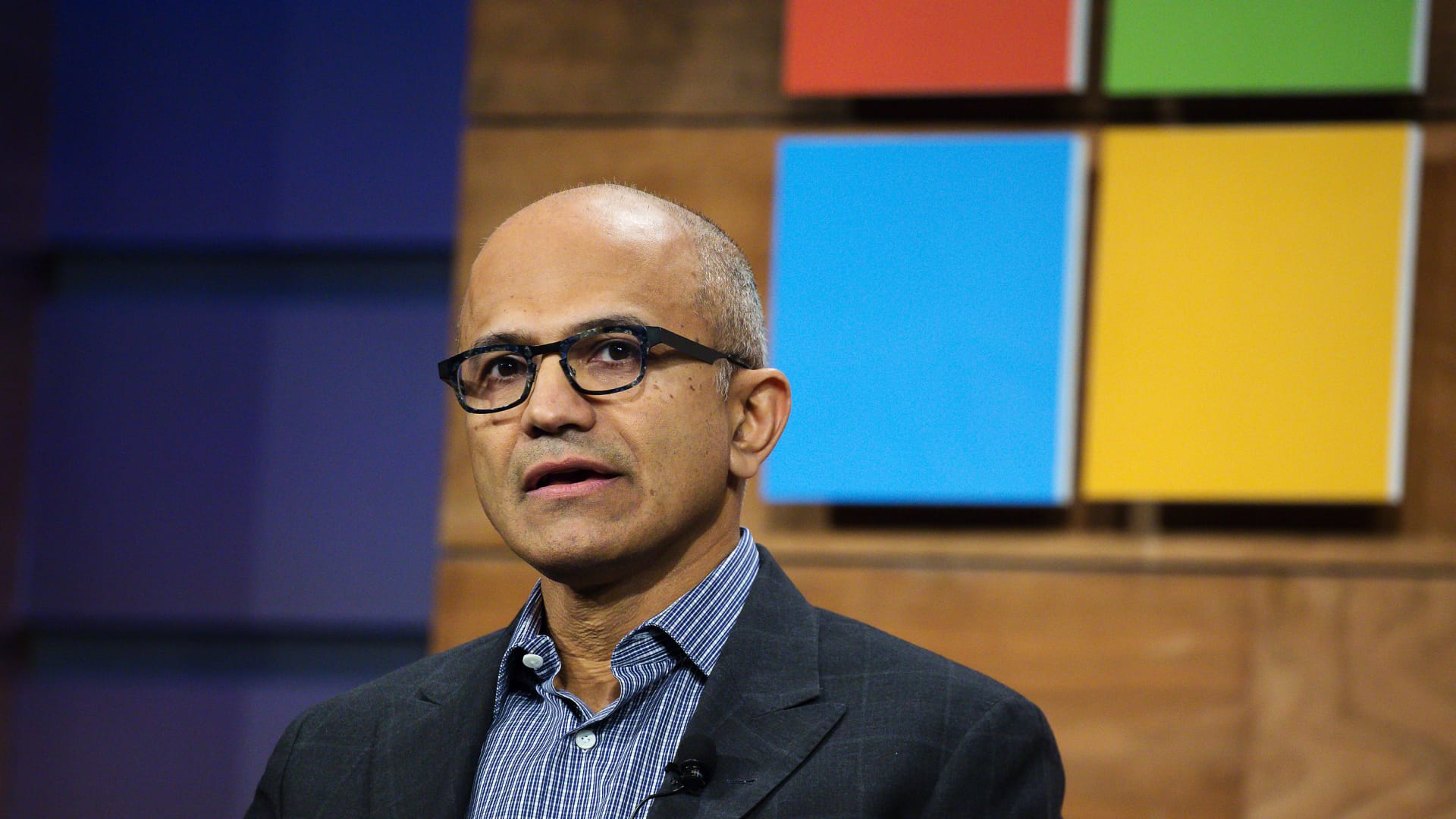
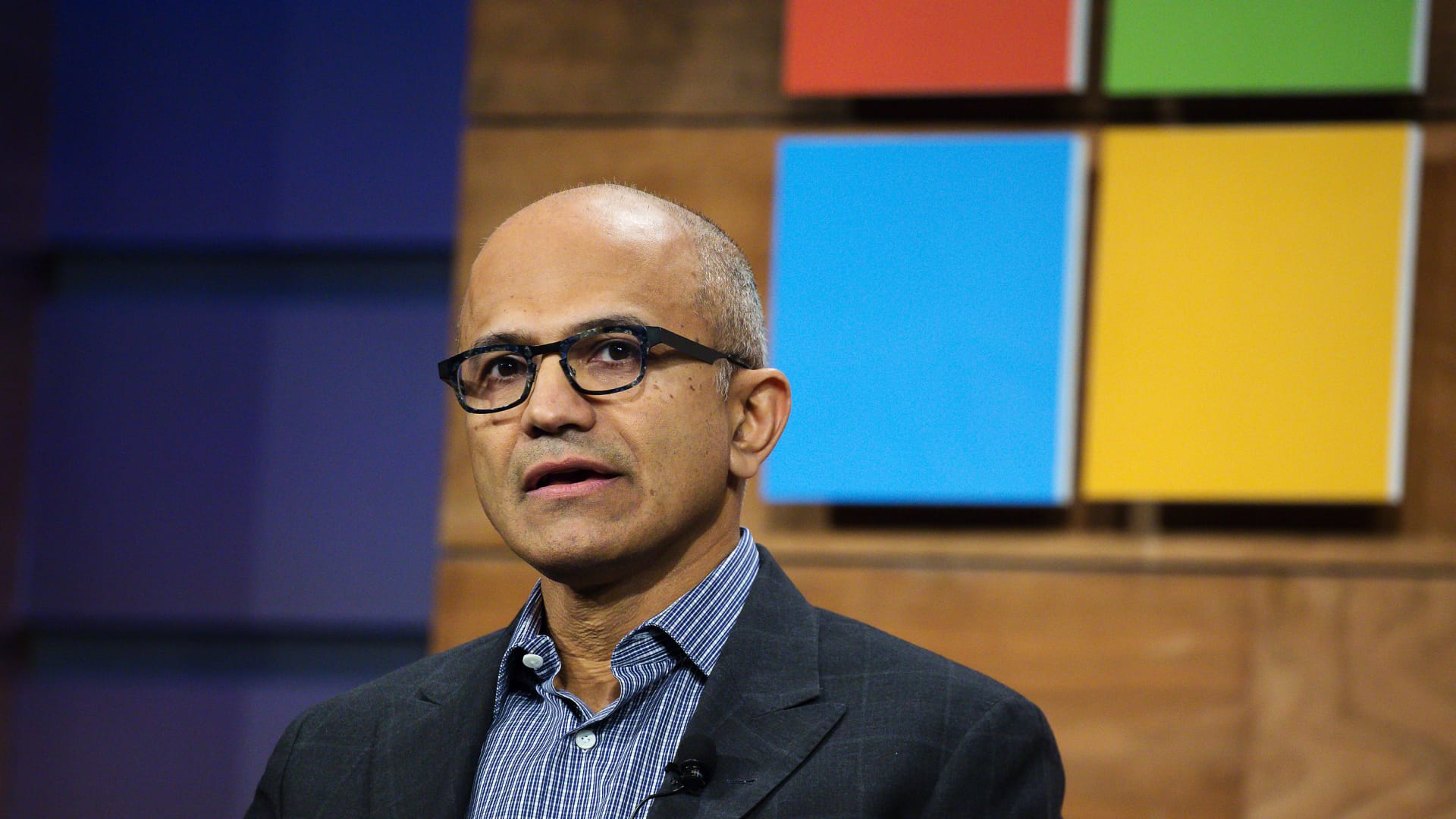
 www.cnbc.com
www.cnbc.com